Bandwidth vs Throughput. Keys to Network Efficiency
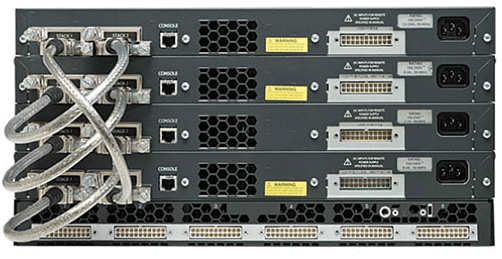
What Is Bandwidth? Bandwidth refers to the maximum amount of data that can be transmitted across a network from a source to a destination within a specified period. It represents the network’s potential capacity for data transfer, typically measured in bits per second (bps). Common units of measurement include kilobits per second (kbps), megabits per second (Mbps), and gigabits per second (Gbps). To visualize bandwidth, think of it as the width of a water pipe: a wider pipe allows more water to flow through simultaneously, just as higher bandwidth enables a network to transport more data at once. Bandwidth reflects the theoretical data transfer limit of a network under optimal conditions. Importance of Bandwidth Bandwidth is a critical factor in determining internet speed and download times. Since it is a limited resource, managing it efficiently is essential. Different devices and applications consume varying amounts of bandwidth, and insufficient bandwidth can lead to network congestion and slow performance. Key Benefits of High Bandwidth Enhanced Online Experiences: High bandwidth allows for faster data transfer, essential for smooth streaming, quick downloads, and responsive web browsing, leading to improved user satisfaction. Multidevice Connectivity: Adequate bandwidth supports multiple devices operating simultaneously on the same network without compromising speed or performance, which is crucial for homes and workplaces. Smooth Video Conferencing: Stable and high-quality video and audio during online meetings depend on sufficient bandwidth, enabling effective remote communication and collaboration. Support for Modern Applications: Emerging technologies such as cloud computing, virtual reality, and IoT require significant bandwidth to function optimally. High bandwidth ensures these applications run seamlessly. Reduced Latency and Congestion: Sufficient bandwidth helps minimize delays and prevents network congestion, ensuring consistent and reliable connectivity even during peak usage periods. Factors Influencing Network Performance The performance of a network depends on several devices and components, including: Network Switches: Devices that efficiently manage data transmission within a network. Routers: Direct data packets between networks. Wireless Access Points: Enable devices to connect to the network wirelessly. Firewalls: Provide security and manage data flow to ensure safe communication. Key Factors Influencing Network Bandwidth and Throughput Key Factors Influencing Network Bandwidth Here are some essential elements that affect bandwidth: Network Infrastructure The network infrastructure, including the types of cables and devices used, significantly influences bandwidth. Fiber optic cables generally offer higher bandwidth compared to copper wires. Additionally, the quality and capability of networking equipment such as routers, switches, and modems can either enhance or limit potential bandwidth. Internet Service Providers (ISPs) ISPs play a crucial role in determining bandwidth by setting limits and offering various service plans. Different packages provide varying levels of maximum bandwidth, with higher-tier plans typically offering faster speeds and more reliable connections. Network management practices like throttling can also affect the user’s bandwidth experience. Network Traffic and Load The amount and type of data being transmitted over the network can impact available bandwidth. Heavy traffic, especially during peak usage times, can cause congestion and slow down data transfer rates. Applications that require high data rates, such as streaming and large downloads, can consume significant bandwidth, impacting other activities. Network Topology and Design The design and structure of a network, including its topology, influence how bandwidth is distributed and utilized. A well-planned network design minimizes potential bottlenecks and optimizes performance. Conversely, complex or poorly configured network structures can lead to inefficient bandwidth usage and degraded performance. Physical and Environmental Conditions Physical distances between devices and infrastructure can impact bandwidth, particularly in networks spanning large geographic areas. Environmental factors such as electromagnetic interference and physical obstructions can degrade signal quality, especially in wireless networks, thus affecting bandwidth availability. User Behavior and Application Demands User activities and the applications they use significantly affect bandwidth. High-demand applications such as video conferencing, online gaming, and cloud services require substantial bandwidth for optimal performance. Additionally, user settings and network practices, such as inefficient Wi-Fi configurations, can influence how effectively bandwidth is utilized. What Is Throughput? Throughput measures the amount of data that successfully travels across a network from a source to a destination within a specified timeframe. It specifically indicates the rate at which data packets or messages arrive at their intended recipient, typically measured in bits per second (bps) or data packets per second (pps). Assessing throughput is essential for evaluating, troubleshooting, and enhancing network performance, as it can help identify the underlying causes of slow or poor connections. When users make requests, such as visiting a website, using an application, making a phone call, or downloading files, they expect prompt and high-quality responses. High throughput signifies that a network is efficiently transmitting a large volume of data per second, thereby fulfilling user requests quickly and contributing to overall performance. Why Throughput Matters High throughput offers numerous advantages to networks: Enhanced Productivity: High-performance switches like the FS S5810-48TS significantly boost productivity by increasing the amount of work completed in a given time. This leads to efficient operations, better resource utilization, and minimized bottlenecks, resulting in higher output and profitability. Cost Reduction: Improving throughput reduces costs by enhancing process efficiency. It enables economies of scale, lowers operational expenses, and optimizes labor, contributing directly to savings and improved profit margins. Competitive Advantage: Higher throughput allows businesses to deliver products and services faster, giving them a competitive edge. This responsiveness helps meet customer demands and adapt to market changes, attracting more clients. Scalability and Growth: High throughput is vital for scalability as businesses expand. It ensures processes can handle increased volumes without compromising quality, supporting long-term growth and market entry. Key Factors Influencing Throughput Here are some elements that affect throughput: Bandwidth Capacity Higher bandwidth allows more data to flow at a given time, directly affecting throughput. Networks with greater bandwidth capacity can handle larger volumes of traffic more efficiently, thus improving overall throughput. Network Latency Latency is the delay in data transmission within a network. High latency can significantly reduce throughput as it slows down the rate at which data packets are delivered. Minimizing latency through optimized routing and faster transmission technologies …
Read more “Bandwidth vs Throughput. Keys to Network Efficiency”